By now everybody must have read the Mat Honan’s heartbreaking story of a hack attack on him which paralyzed his online life completely, not only his online accounts were hacked but because of the recent cloud integration of almost all services, devices and various other things, he ended up losing his data too.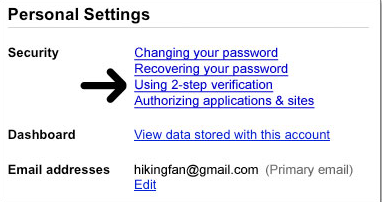
This story not only made us aware of the possible security threats we live under to our lives but also exposes some very cruel and dangerous vulnerabilities which could put our accounts in danger. Amazon very quickly changed a few many things to avoid any such issues and Apple too took a very big step and now doesn’t allow any password reset requests via phone.
Being aware of such harmful and hideous activities, Google had long ago announced the 2-step authentication system which not only keeps your account more secure but also makes it easy to keep track of your logins and also gives some brilliant solutions in case you think your accounts are in trouble.
The 2-step authentication is part of the two-factor authentication system, very simply two-factor authentication means “something you know” ( like your password ) and “something you have” ( like your phone ).
To make things simple, here is a video demo :
Myth #1: But what if my cell phone doesn’t have SMS/signal, or I’m in a foreign country?
Reality: You can install a standalone app called Google Authenticator (it’s also available in the App Store), so your cell phone doesn’t need a signal.
Myth #2: Okay, but what about if my cell phone runs out of power, or my phone is stolen?
Reality: You can print out a small piece of paper with 10 one-time rescue codes and put that in your wallet. Use those one-time codes to log in even without your phone.
Myth #3: Don’t I have to fiddle with an extra PIN every time I log in?
Reality: You can tell Google to trust your computer for 30 days and sometimes even longer.
Myth #4: I heard two-factor authentication doesn’t work with POP and IMAP?
Reality: You can still use two-factor authentication even with POP and IMAP. You create a special “application-specific password” that your mail client can use instead of your regular password. You can revoke application-specific passwords at any time.
Myth #5: Okay, but what if I want to verify how secure Google Authenticator is?
Reality: Google Authenticator is free, open-source, and based on open standards.
Myth #6: So Google Authenticator is a free and open-source, but does anyone else use it?
Reality: Yes! You can use Google Authenticator to do two-factor authentication with LastPass, WordPress, Amazon Web Services, Drupal, and DreamHost, or even use a YubiKey device. There’s even a Pluggable Authentication Module (PAM) so you can add two-factor authentication to any PAM-enabled application. That means you can use Google Authenticator to add two-factor authentication to SSH, for example.
One last tip: use a different password on Gmail/Google than on other services. If you reuse a password and a hacker cracks into one company, they can use the same password to crack into your Google account.
Please don’t wait to turn on 2-step verification. It’s not that hard, and it will really protect your account. Why not set up two-step authentication right now?
